Office 365 Advanced Threat Protection 101: ATP
(Safe Attachment Policies)

Previously, in Part 1 of this Office 365 Advanced Threat Protection 101 article series, we explored how to take your first steps into making your mailboxes more secure by reducing the number of phishing e-mails sent to your users with ATP Anti-Phishing policies. Now in Part 2, we will explore ATP Safe Email Attachments, which checks to see if email attachments or files are malicious and protects your organization according to the ATP Safe Attachments policy configured by you, the Office 365 administrator.
In this article, we’ll discuss how to create an ATP Safe Attachment policy and how to enable ATP protection to files in Microsoft SharePoint Online, OneDrive for Business, and Microsoft Teams. Note that I won’t be going into detail of how ATP Safe Attachments works in this article, as Microsoft has already made a great article here.
In this scenario, I’m assuming you have an Office 365 tenant with Exchange Online, and you’ve already purchased ATP licenses and have assigned them to your users.
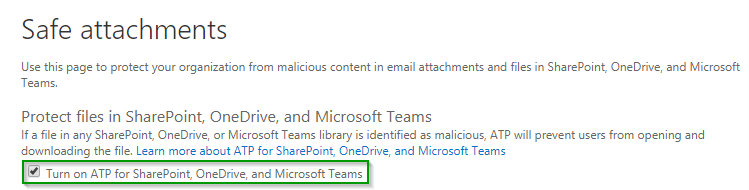
Enabling SharePoint, OneDrive, and Microsoft Teams Protection
Similar to my previous article on ATP Anti-Phishing Policies, we’ll want to head over to the Office 365 Security & Compliance Center, then go Threat Management, then go to Policy in the side navigation bar. Then click on the ATP Safe Attachments tile.

At the Safe Attachments policy page, the first thing you want to do is turn on ATP for SharePoint, One Drive, and Teams. This will just add another layer of protection in case a malicious file is shared in one of these services.
Creating Your First ATP Safe Email Attachments Policy
In this scenario, we’ll be creating an ATP Safe Attachments Policy that:
- This applies to the imaginet.com mail domain
- Delivers the message immediately and scans the attachment. If the attachment contains malware, send it to quarantine.
At the Safe Attachments Policy Page, click the Create button to create a new policy. When the new window pops up, specify your Policy Name and Description.
In this next section, we’ll be selecting the malware response; this part of the policy tells ATP what you want to do with an attachment that has been scanned and found to contain malware. Your options are:

You’ll find that you can redirect an attachment to another user, although I don’t see myself or team reviewing these attachments individually. I’ll leave this unchecked.

Then specify who this policy will apply to. In this scenario, I’ll be applying this policy to imaginet.com.

Review your changes, and click Save to create the policy. Microsoft mentions that this may take up to 30 minutes to affect.
How Does This Impact My Users?
In the real world, you may want to test this policy by applying it to a test user or pilot group before applying it to the entire organization.
The policy we just created uses Dynamic Delivery which, according to Microsoft does not cause email delivery delays since the message is sent to the recipient right away, and a placeholder file is attached until the email attachment is scanned. While the file is scanned, users can preview the file safely in safe mode. This preview feature supports most PDFS and office files. If an email attachment contains malware, it’s sent to quarantine. This allows users to receive the email message right away and preview the message safely while it is being scanned.
You may be wondering: what if an attachment was sent to the quarantine by mistake due to a false positive? Well, being an Office 365 administrator, you should be familiar with the Exchange Online quarantine by now. Here you’ll be able to review the message and determine for yourself if the message is a false positive, and if it is, you’ll be able to release it back to the user.
Coming Up Next
Next, in Part 3 of this Office 365 Advanced Threat Protection 101 article series, we will explore Office 365’s ATP Safe Links Policies, which can help protect your organization by providing verification of URLS in email messages and Office documents. And as always, if you need help with your Office 365 environment, Imaginet is here for you. Our Imaginet certified Office 365 experts can assist you with any of your Office 365 initiatives. To find out more, schedule your free consultation call with Imaginet today.
Thank you for reading this post! If you enjoyed it, I encourage you to check out some of our other content on this blog. We have a range of articles on various topics that I think you’ll find interesting. Don’t forget to subscribe to our newsletter to stay updated with all of the latest information on Imaginet’s recent successful projects

discover more
SQL Saturday Part 2: Learning About Microsoft Fabric
SQL Saturday Part 2: Learning About Microsoft Fabric February 29, 2024 I’ve been digging into Microsoft Fabric recently – well overdue, since it was first released about a year ago.…
My Trip to SQL Saturday Atlanta (BI Edition): Part 1
My Trip to SQL Saturday Atlanta (BI Edition): Part 1 February 23, 2024 Recently, I had the opportunity to attend SQL Saturday Atlanta (BI edition), a free annual event for…
Enabling BitLocker Encryption with Microsoft Intune
Enabling BitLocker Encryption with Microsoft Intune February 15, 2024 In today’s data-driven world, safeguarding sensitive information is paramount, especially with the increase in remote work following the pandemic and the…
Let’s build something amazing together
From concept to handoff, we’d love to learn more about what you are working on.
Send us a message below or call us at 1-800-989-6022.